When you think of cyberattacks, you might imagine a hacker in a solitary room, staring at a computer screen filled with lines of code, typing away to break into your network. However, in reality, it is more likely that a cybercriminal will try to manipulate your actions, rather than your software, to gain access to your data.
Hackers will often prey on the different facets of human emotion and psychology, such as curiosity, greed, fear and even empathy, to get you to carry out specific actions such as revealing your password or giving them access to your computer or business’ networks.
This act of exploiting human psychology, as opposed to technical hacking, is known as ‘social engineering’. Cyberattackers will more often utilise social engineering attacks instead of technical hacking, because:
- People have a natural tendency to trust others – an attribute which can be easily exploited by malicious actors.
- Social engineering attacks do not require sophisticated technical cybersecurity skills, but instead rely on capitalising on human error.
Therefore, it is important for members of a business, especially security personnel, to know when a person is who they say they are. Physical security becomes meaningless when you allow a person to walk into your business and access computers or your network without first verifying the legitimacy of their identity. The same idea applies online too – whenever you receive a message from someone think: “Is this person who they say they are?” and “How can I verify whether what they’re saying is true?”. As a rule, you should not accept an unsolicited message at face value.
What Happens during a Social Engineering Attack?
There is a concept known as the Social Engineering Life Cycle, which outlines the four stages of a social engineering attack:
Stage 1: Investigation
This stage involves identifying the victim(s) and gathering background information. Criminals can take weeks or months researching a business to learn enough to make their lies convincing. This preparation may include things like researching employees on social networking sites like LinkedIn or following employees on Facebook to take advantage of any business information they may post. As such, it is important that you ensure that your social media posts do not accidentally reveal information that can be utilised by attackers, like employee details or organisational charts.
Stage 2: Hook
The hook is where attackers will use the information they’ve gathered to engage the victim and take control of the situation. This is the stage that they will create a convincing story, often tailored to their victim. An example of a hook is when an attacker sends a phishing email to an employee of a business, posing as their manager, which tells them that they have been given a promotion, and that they need to click a malicious link to accept.
Stage 3: Play
After the hook is successful, the attacker then executes the attack in this stage. After the victim has given the attacker access to their business, the attacker then can choose to siphon data or disrupt the business through means such as ransomware.
Stage 4: Exit
Once the attacker feels like they have obtained all the data they need, they will cease the interaction as well as remove all traces of malware to cover up their tracks.

What Does a Social Engineering Attack Look Like?
Since social engineers rely upon human error and convincing people that their identity is legitimate, attacks are not limited to happening online. Using the information they have gathered during the investigation stage, they can infiltrate a business in various ways that may not be obvious.
1. In-Person Attacks
Attackers can physically enter a business and gain access to its network using devious tactics. For example, they may purchase a T-shirt that has the same brand as the devices the business uses, and then pose as tech support. They may say things like “Sorry, can you hold the door? I forgot my key card today”. Attackers might even research key employees and refer to them by name to make it seem like they are part of the company. Using these tactics, attackers would then be able to access devices without raising suspicion. From here, they can install malware and access and manipulate the company’s data as they please.
2. Online Attacks
The trend of businesses going online has meant that cyberattacks happen more frequently. As businesses and employees engage with social networking sites, personal details and company information is publicly revealed, allowing attackers to easily find plenty of detailed information that can help them to create convincing narratives. The following are common social engineering attacks that occur online:
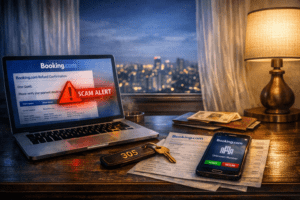
Phishing
Phishing is the most common type of social engineering scam. In 2020, the number of phishing attacks reported increased by 75% compared to 2019 (Source), demonstrating just how effective and convincing these attacks can be. Phishing campaigns involve imitating a legitimate source, such as the victim’s bank or company and creating a narrative that seems logical enough to warrant the victim sending over sensitive personal data, including login credentials. Phishing messages may:
- Create a sense of urgency. The message may tell you that someone you know urgently needs help and prompts you to send money to the criminal.
- Ask you to verify your information. The attackers may pose as the victim’s bank and ask them to click a malicious link or verify their login credentials by sending these back to the attacker. These messages also tend to convey urgency, to make the victim act before thinking.
- Notify you that you’ve won a prize. The message might claim that you’ve won the lottery, or that you’ve inherited money from a relative. The message will then ask for your banking details including things such as passwords so that they can ‘send you the money’. In reality, by providing your banking details, the attackers can access your accounts and steal your money.
A common subtype of phishing attacks that primarily affects employees of a business is known as ‘spear phishing’. This is where an attacker poses as a senior manager or coworker, and then asks the victim for sensitive company information pertaining to the business’ finances, projects or employee details, under the guise that the email is just a day-to day business inquiry.
Baiting
In baiting attacks, false promises are used to appeal to a victim’s curiosity or greed. Baiting often takes place on websites offering a free download of something that the victim wants, like a new movie or music, but can also occur as ‘too good to be true’ deals on auction sites. People who take the bait find their devices infected with malware, or, if they paid for the fake deal, lose their money without receiving the item.
Scareware
Scareware attacks play on the emotion of fear, bombarding victims with false alarms and fake threats. A common scareware scam you may have seen before is “Your computer is infected with a virus!”. The scareware then prompts you to install a scanning tool or antivirus software to fix this, which in reality is malware. As a rule, do not click on any pop-up messages telling you to install software on your device.
3. Protecting Yourself
While social engineering tactics are devious and can be hard to spot, there are methods and steps you can take to prevent being scammed. The following are some practical tips you can use to help you and your business to defend against social engineering:
- Think before you act. Scammers use urgency in their messages to get you to act on impulse and send personal information. Never let the urgency of a message dictate your actions and don’t open unexpected attachments or links.
- Verify the message using your own research. You should always check the legitimacy of a message if it looks like it came from a company or bank you use. You should use a search engine to go to the institution’s real website or call the institution using the number on their website to verify the message.
- Reject requests for personal information. Financial institutions never ask for personal account details such as passwords or security questions through email or text.
- Utilise the spam filters on your email addresses and set them to high. This can help to filter out emails that have been detected to be spam. Be sure to check the spam folder.
- Keep your devices secure and up to date. Install antivirus software on your computers and smartphones to detect any malware that has potentially infected them. Some antivirus software may also include anti-phishing web extensions, so utilise these to help you keep an eye out online.
- Have a training program to increase cyber awareness. Make sure your company has a comprehensive training system that raises cybersecurity awareness and teaches employees how to spot and avoid common attacks. The best systems also include phishing testing to ensure employees are more resistant to attacks.