JUN 26, 2022
Earlier this year, an industry report stated that 79% of businesses remain concerned about the security risks of an increasingly remote workforce. Cyberattacks are on the rise since the COVID-19 pandemic, in part because many organizations fail to put in place adequate cybersecurity measures and procedures.
In addition, there is a worldwide shortage of cybersecurity professionals in every industry. The investment in educated cybersecurity professionals is vital to protecting your remote workforce from a cyberattack. They can help put an updated cybersecurity strategy in place, and train employees about staying safe online and so much more.
Reassess Your Cybersecurity Strategy
Cybercriminals are constantly evolving their tactics, and businesses need to keep up with security measures. There are even more vulnerabilities with a remote workforce, such as the use of personal devices, and working on unsecured networks. Organizations must update their cybersecurity strategy continually to stay current. As stated in the TechTarget guide, a cybersecurity strategy “is a high-level plan for how your organization will secure its assets during the next three to five years.”
The first step to building a cybersecurity strategy is assessing the threat landscape. Then, assess your current strategy — determine if you have the right programs and applications to protect your employees. Is your IT team able to execute an effective strategy with the resources they’re allocated? Once you have a clear picture of your current status, you can explore ways to update and improve your cybersecurity strategy, ideally focusing as much or more on preventing possible cybercrimes than reacting to them. Make sure to document your strategy and update all pertinent employees. Don’t forget — part of your cybersecurity strategy should be training for your employees.
Employee Cybersecurity Training
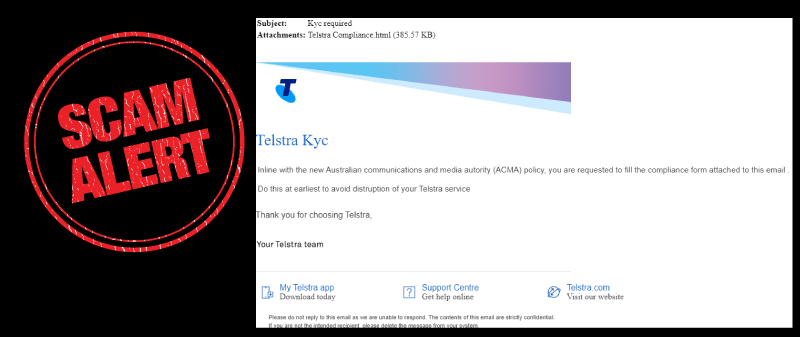
There are a variety of free and paid cybersecurity employee training programs available, both online and in-person. Cybersecurity training should be ongoing for your entire team and should be part of the orientation process for new employees. Ongoing training should include, but not be limited to education about:
- Types of security threats (malware, phishing, ransomware).
- Password management and security.
- Malicious links.
- Logging on from a personal device or a device outside the network.
- How to spot suspicious behavior.
- What to do if they suspect they have been targeted by a cybercriminal
Implement Remote Desktop Setup and Multi-Factor Authentication
To protect against the increased risks presented by remote and hybrid employees, it’s recommended for them to use a remote desktop setup, such as a VPN, and Multi-Factor Authentication (MFA). With MFA, a user must provide two or more verification methods to successfully log in. In fact, Microsoft engineers said that 99.9% of compromised accounts don’t use MFA.
Never Work on an Unsecure Network
For remote employees, “working from home” can often mean “working from a coffee shop.” When working on a secure (password protected) network, data is encrypted — as opposed to plain text data. Plain text data can be intercepted by almost anyone with basic malicious cybersecurity knowledge. Encrypting data increases security immensely. This applies to mobile devices and tablets, in addition to laptops. Even checking email on a mobile device on an unsecured network can lead to a security compromise.
Use a Zero Trust Framework
Zero trust frameworks are important, especially with remote workers. The zero trust model follows the idea that all people and devices attempting to join a network may be hostile and must be authenticated at every access point and unique activity. This includes users inside and outside of the network, and cloud-based or local users.
An IBM report states that compromised credentials were responsible for about 20% of data breaches in 2021, costing an average amount of $4.37 million per breach. The average cost of a data breach was $1.76 million less at organizations that applied a zero trust approach.
Improved Password Management and Security
You’ve heard it before, but it’s worth repeating — don’t use “password” as your password. The same goes for “password1” and “1234.” There are multiple algorithms that criminals can use to guess commonly used passwords. Here are a few password best practices:
- Use different passwords for different logins.
- Don’t use personal information in your password (pet or street names, or important dates).
- Never share your password with anyone.
- The longer the password, the harder it is to guess.
- If you want to store passwords, do so in a secure password management system.
A cyberattack can be devastating to an organization. Protecting your remote workforce’s online activities from cybercrime must be a focus for organizations. It starts with having the right cybersecurity professionals, setting a cybersecurity plan and educating employees on staying safe when working from home. Having a plan in place can help keep your business, data and employees safe.
#cybertraining #cybersecurity #psybersecurity #cybermate #cybercrime #humanrisk #behaviouralrisk #sme #cybersafe #cybercompliance